What is a monitored alarm? A guide for business security
- Sam Myles
- Mar 21
- 8 min read

Many business owners believe all alarm systems offer equal protection, but that assumption can leave facilities vulnerable. Monitored alarms provide continuous oversight through professional centres that respond immediately to threats, unlike standard alarms that simply sound locally. Understanding how monitored systems work and their specific advantages helps you make informed decisions about facility security and regulatory compliance. This guide explains what monitored alarms are, their key benefits for businesses, available monitoring technologies, and practical installation considerations to strengthen your security infrastructure.
Table of Contents
Key Takeaways
Point | Details |
Definition and features | Monitored alarms connect your security system to a professional monitoring centre that receives instant alerts when sensors detect threats, providing continual oversight beyond local sounders. |
Real time response | Round the clock monitoring reduces detection to response time and enables emergency services to be dispatched while alerting management. |
Monitoring technologies | Cellular, IP and traditional phone line options, plus hybrids, offer varying reliability and management capabilities depending on infrastructure and backup needs. |
Installation and maintenance | Plan multiple communication paths and carry out regular maintenance to prevent tampering and ensure continuous monitoring. |
What is a monitored alarm and how does it work?
A monitored alarm connects your security system directly to a professional monitoring centre that receives instant alerts when sensors detect threats. Unlike standalone alarms that only sound on-site, these systems transmit signals through dedicated communication channels to trained operators who assess situations and coordinate appropriate responses.
When an event occurs, sensors trigger the alarm panel, which immediately sends coded signals to the monitoring station. Operators receive detailed information about the alert type, location, and timestamp. They follow established protocols to verify the threat, attempt contact with designated keyholders, and dispatch emergency services if needed. Monitored alarms provide continual surveillance and immediate alert to security providers when triggered, ensuring no incident goes unnoticed regardless of time or day.
Transmission methods vary based on infrastructure and reliability needs:
Cellular monitoring uses mobile networks to send encrypted signals, offering independence from physical connections
IP monitoring leverages internet connections for fast, reliable data transmission with remote system management
Traditional phone lines provide basic connectivity but face vulnerability to physical tampering
Hybrid systems combine multiple channels to ensure backup communication if primary methods fail
Monitoring centres respond to various trigger events including intrusion detection, fire alarms, environmental hazards like flooding or temperature extremes, and panic button activations. Each alert type follows specific response protocols tailored to the threat level and business requirements.
Pro Tip: Configure your system with multiple communication paths to prevent criminals from disabling monitoring by cutting a single connection point.
The fundamental difference from non-monitored alarms lies in professional intervention. Standard systems rely entirely on someone hearing the alarm and taking action. Monitored systems guarantee trained personnel receive alerts and initiate responses even when your premises are empty or during overnight hours when local alarms might go unheard.
Key benefits of monitored alarm systems for business security
Round-the-clock professional surveillance transforms how businesses protect assets and maintain operations. Monitoring centres never close, providing constant vigilance that human security staff cannot match economically. This continuous oversight dramatically reduces the window between threat detection and response, minimising potential losses from theft, vandalism, or fire damage.
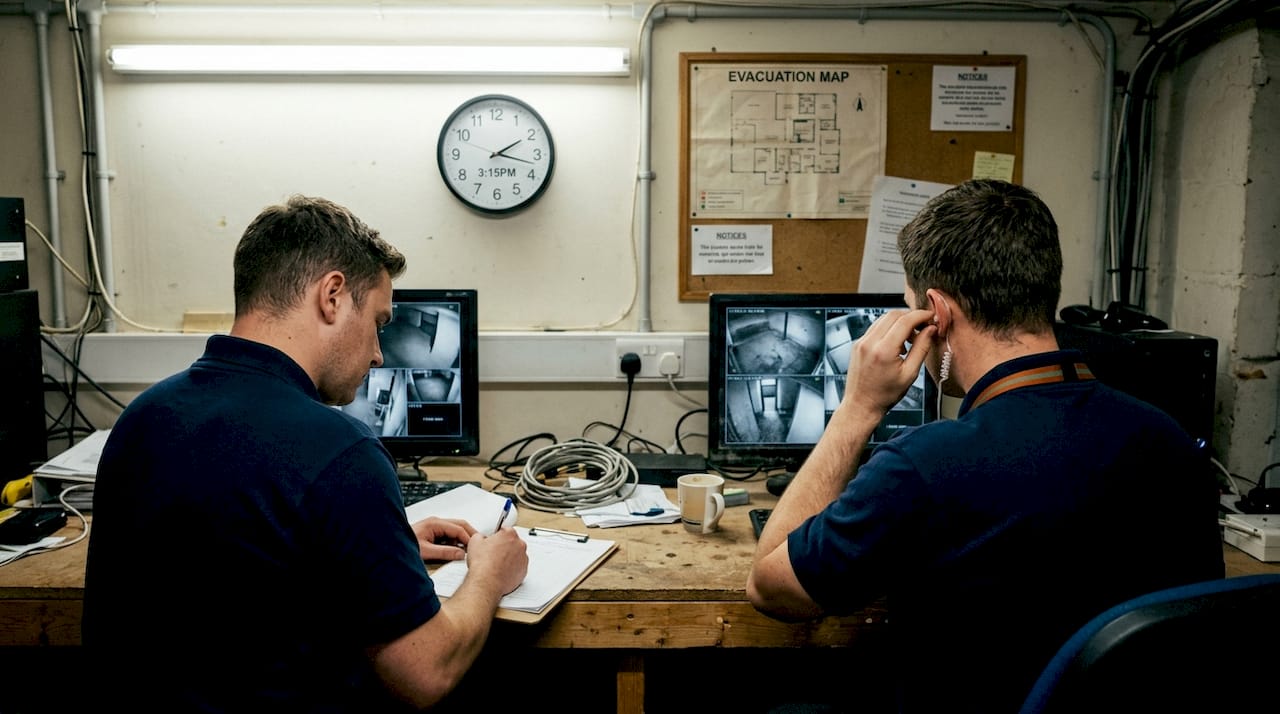
Real-time monitoring significantly reduces response time and potential loss in security breaches. When seconds matter, professional operators can dispatch emergency services whilst simultaneously alerting your management team. This coordinated response often prevents minor incidents from escalating into major losses. Insurance companies recognise this value, frequently offering premium reductions for businesses with certified monitored systems.
Compliance requirements drive many businesses towards monitored alarms. Industry regulations and insurance policies increasingly mandate professional monitoring for certain facility types or asset values. Documentation from monitoring centres provides verifiable proof of security measures, satisfying auditors and insurers. You maintain detailed records of all alerts, responses, and system tests without additional administrative burden.
Remote access capabilities extend monitoring benefits beyond threat response:
View real-time system status from any location through secure web portals or mobile applications
Arm or disarm systems remotely when staff schedules change unexpectedly
Receive instant notifications about system events directly to your devices
Grant or revoke access permissions without physical visits to update hardware
Review historical data to identify patterns or vulnerabilities in security procedures
Integration with broader security infrastructure amplifies protection. Modern monitored systems connect seamlessly with CCTV cameras, access control systems, and environmental sensors. When an alarm triggers, operators can immediately review camera feeds to verify threats before dispatching resources. This integration reduces false alarm costs whilst improving response accuracy.
Professional monitoring transforms alarms from simple warning devices into comprehensive security management systems with documented accountability.
Pro Tip: Request monitoring centre certifications and ask about operator training programmes to ensure you receive professional-grade service quality.
Peace of mind represents an often-overlooked benefit. Business owners gain confidence knowing experts monitor their facilities continuously. You focus on operations rather than worrying about security gaps during holidays, weekends, or after-hours periods when premises sit empty.
Types of monitored alarm monitoring technologies
Cellular monitoring has become the preferred choice for modern installations. Mobile networks provide reliable signal transmission without dependence on internet connections or phone lines that criminals can easily disable. Encrypted communication protects data privacy whilst cellular backup ensures monitoring continues even during power outages when paired with battery systems. Monthly cellular service fees typically range lower than traditional phone line costs, though initial equipment expenses run slightly higher.
IP monitoring offers the fastest data transmission and richest feature sets. Internet-based systems support real-time video verification, remote system management, and integration with cloud-based security platforms. Different transmission methods offer varied reliability and costs, with IP monitoring excelling in bandwidth and functionality. However, dependence on internet stability presents risks in areas with unreliable broadband service. Power outages that affect routers can interrupt monitoring unless backup power protects network equipment.
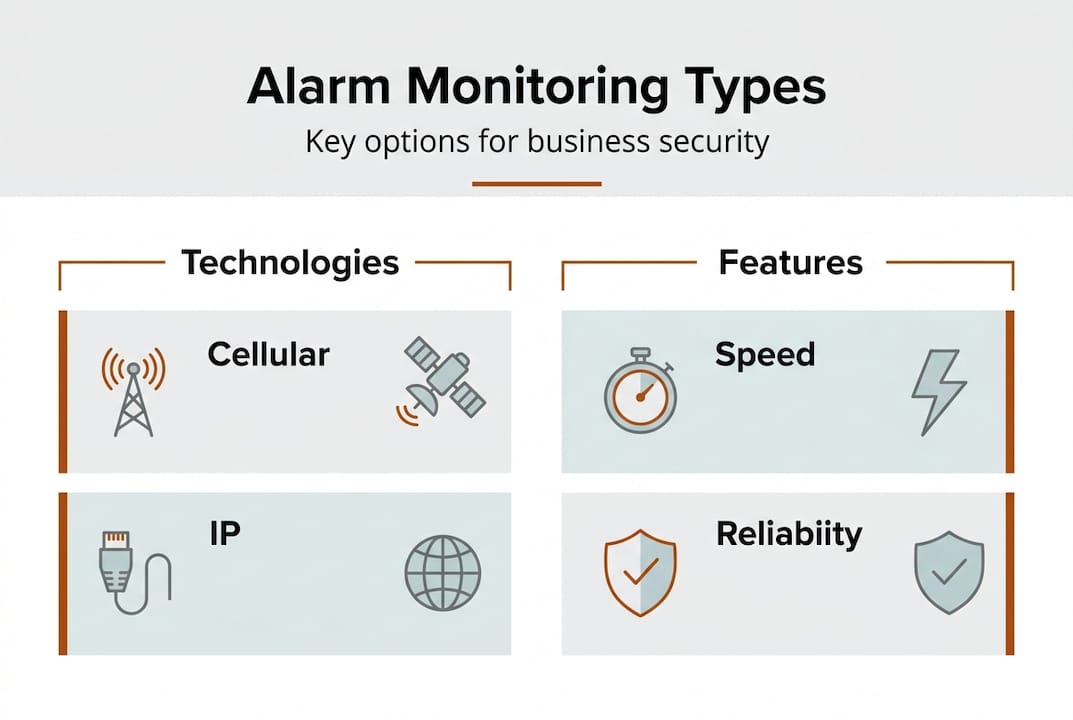
Traditional phone line monitoring represents the oldest technology, still found in legacy installations. Dedicated landlines provide stable connections but face significant vulnerabilities. Criminals can cut external phone lines to disable monitoring before attempting break-ins. Monthly line rental costs often exceed cellular or IP alternatives. Phone line monitoring suits only specific scenarios where other technologies prove unavailable or existing infrastructure makes replacement impractical.
Technology | Reliability | Speed | Vulnerability | Monthly cost |
Cellular | High | Fast | Low | Moderate |
IP | Very high | Very fast | Moderate | Low to moderate |
Phone line | Moderate | Slow | High | Moderate to high |
Hybrid | Excellent | Fast | Very low | Higher |
Hybrid systems combine multiple technologies to eliminate single points of failure. A typical configuration uses IP monitoring as the primary channel with cellular backup. If internet connectivity fails, the system automatically switches to cellular transmission without interrupting monitoring service. This redundancy provides maximum reliability for high-security applications or facilities in remote locations.
Choosing appropriate technology depends on several business factors:
Location infrastructure availability and reliability of internet or cellular coverage
Budget constraints for initial installation versus ongoing operational costs
Security requirements and acceptable risk levels for your specific industry
Integration needs with existing security systems and management platforms
Regulatory compliance mandates that may specify monitoring technology standards
Pro Tip: Survey your location’s cellular signal strength and internet reliability before selecting monitoring technology to avoid connectivity issues after installation.
Installing and maintaining monitored alarm systems for compliance and security
Selecting a certified installer ensures your system meets regulatory standards and performs reliably. Look for companies holding relevant accreditations from industry bodies and insurance-recognised certifications. Certified installers understand compliance requirements specific to your industry and design systems that satisfy both security needs and legal obligations. Request references from similar businesses and verify the installer’s monitoring centre partnerships.
Professional site assessments form the foundation of effective security. Experienced installers evaluate your facility’s unique vulnerabilities, entry points, and operational patterns. They identify optimal sensor placements, communication technology requirements, and integration opportunities with existing systems. Professional installation and regular maintenance are essential for system reliability and compliance. Custom design ensures coverage addresses your specific risks rather than applying generic templates.
Installation follows a structured process:
Conduct comprehensive site survey documenting all access points and vulnerable areas
Design system layout specifying sensor types, quantities, and strategic placement locations
Install control panels, sensors, and communication equipment according to manufacturer specifications
Configure monitoring centre connections and test all signal transmission paths
Programme user codes, access schedules, and response protocols tailored to operations
Train designated staff on system operation, arming procedures, and emergency responses
Document installation details and provide compliance certificates for insurance and regulators
Regular maintenance prevents system failures during critical moments. Schedule professional inspections quarterly or semi-annually depending on system complexity and environmental conditions. Technicians test all sensors, verify communication channels, replace batteries, and update software. Maintenance visits provide opportunities to adjust system settings as your business evolves or operational patterns change.
Staff training ensures humans support rather than undermine security technology. Employees must understand proper arming and disarming procedures to prevent false alarms that waste resources and incur fees. Designate primary and secondary keyholders who monitoring centres can contact for verification. Review response protocols annually so staff know exactly how to react during genuine emergencies.
Pro Tip: Maintain a dedicated security logbook documenting all system tests, maintenance visits, and alarm events to demonstrate compliance during insurance reviews or regulatory audits.
Documentation requirements extend beyond installation certificates. Retain records of all monitoring centre communications, response times, and incident reports. These documents prove your security measures function as intended and provide evidence for insurance claims if losses occur. Regular testing generates documentation showing ongoing system reliability rather than just initial installation compliance.
Enhance your business security with Signal Fire & Security monitored alarms
Protecting your facility requires more than installing equipment and hoping it works when needed. Signal Fire & Security delivers comprehensive monitored alarm solutions designed specifically for Irish businesses. Our certified technicians assess your unique security challenges and design systems that address vulnerabilities whilst satisfying compliance requirements.

We specialise in professional intruder alarm installation integrated with 24/7 monitoring services. Our systems use redundant communication technologies ensuring alerts always reach our monitoring centre regardless of connectivity issues. You gain peace of mind knowing trained operators oversee your premises continuously, ready to coordinate emergency responses the moment threats emerge.
Discover why businesses throughout Dublin trust Signal Fire & Security for critical security infrastructure. Our maintenance programmes keep systems operating reliably whilst documentation services ensure you meet insurance and regulatory obligations. Contact us today for a comprehensive security assessment and customised monitoring solution that protects your assets, employees, and operations.
Frequently asked questions about monitored alarms
What differentiates a monitored alarm from a standard alarm?
Monitored alarms connect to professional centres that receive instant alerts and coordinate responses, whilst standard alarms only sound locally. Professional monitoring ensures threats receive immediate attention even when premises are unoccupied. You gain documented security oversight that satisfies insurance and compliance requirements.
Can monitored alarms reduce insurance premiums?
Yes, most commercial insurers offer premium reductions for certified monitored alarm systems. Reductions typically range from 10% to 25% depending on system specifications and monitoring service quality. Request documentation from your monitoring provider to submit with insurance applications or renewal negotiations.
How fast can response teams react to alarm triggers?
Monitoring centres typically assess alerts and initiate contact within 30 to 60 seconds of receiving signals. Emergency service dispatch follows immediately after threat verification, usually within two to three minutes total. Response times depend on verification protocols and emergency service availability in your location.
Is remote monitoring available with all monitored alarms?
Most modern systems include remote access through web portals or mobile applications as standard features. You can view system status, arm or disarm remotely, and receive instant notifications. Older systems may require upgrades to enable remote capabilities, so confirm features when selecting monitoring services.
What are common false alarm causes and how are they handled?
User error during arming or disarming accounts for most false alarms, followed by environmental factors like insects or temperature changes affecting sensors. Monitoring centres attempt keyholder verification before dispatching services to reduce false alarm costs. Regular maintenance and proper staff training significantly reduce false alarm frequency whilst some areas impose fees for excessive false dispatches.
Recommended


Comments